
How AI Is Changing Cybersecurity in 2026 | Full Guide
Just imagine waking up on a morning & discovering that your company’s entire client database record has been misused, _ Not by a team of hackers working for days, but by an automated AI system that slipped past the thousands of organizations that are facing right now.
Understanding how AI is changing cybersecurity in 2026 is no longer optional for IT professionals, business owners, or everyday internet users. It is a matter of survival in an era where both attackers and
Defenders are racing to harness the power of artificial intelligenceIn this guide, you will learn exactly how AI is evolving every corner of the cybersecurity landscape — from
threat detection and automated response to the dark side of AI-powered attacks. Whether you are a security
professional or a curious reader, this article gives you a complete, practical picture.
TABLE OF CONTENTS:
|
. How AI Is Being Used to Defend Against Cyber Threats |
. Frequently Asked Questions (People Also Ask) |
|
. Expert Tips: Getting AI Cybersecurity Right |
. The Dark Side: How Hackers Are Using AI |
|
. AI-Powered Threat Detection and Response |
. AI-Powered Threat Detection and Response |
|
. Machine Learning in Network Security |
. Zero-Day Vulnerabilities and AI Defense |
|
. AI in Security Operations Centers (SOC) |
. Machine Learning in Network Security |
|
. Key AI Cybersecurity Tools in 2026 |
. Common Mistakes to Avoid |
|
. Media, Links & References |
.Conclusion |
-
- The Rise of AI in Cybersecurity
Artificial intelligence has gone from a buzzword to the backbone of modern cybersecurity infrastructure. Over
Over the past three years, AI adoption in security tools has grown by more than 300%, driven by the sheer volume
and the sophistication of cyber threats
Traditional rule-based security systems simply cannot keep pace. They rely on known signatures and
patterns — but attackers have learned to operate outside those patterns. AI changes the game by learning,
adapting, and predicting threats before they fully materialize.
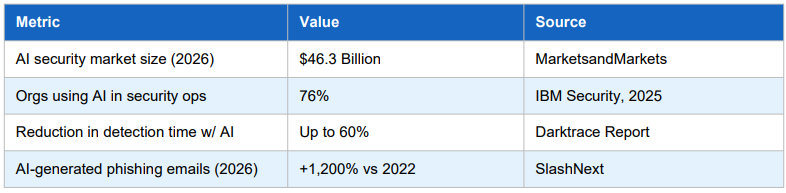
The key drivers behind this rapid rise include the explosion of IoT devices, the shift to remote and hybrid
work, cloud infrastructure complexity, and the growing professionalism of cybercriminal organizations
On the defensive side, AI is a force multiplier. Security teams that once needed dozens of analysts to monitor
A network can now deploy AI-powered platforms that work continuously, without fatigue, bias, or oversight gaps. Core Defensive Applications
The defensive side, AI is a force multiplier. Security teams that once needed dozens of analysts to monitor
a network can now deploy an AI-powered agent that works 24/7, without fatigue, bias, or oversight, nonstop
-
- Behavioral Analytics:
AI baselines normal user and device behavior, then flags in real time— catching insider threats that rule-based systems miss entirely.
- Behavioral Analytics:
-
- Predictive Threat Intelligence:
-
- Machine learning models analyze global threat feeds, dark web data, and vulnerability databases to predict what attackers will target next.
-
- Predictive Threat Intelligence:
-
- Automated Patch Prioritization:
-
- AI ranks vulnerabilities by exploitability and business impact, helping with automated patching
- Prioritization:
-
- AI ranks vulnerabilities by exploitability and business impact, helping
Lean security teams focus patching efforts where it matters most.
- AI ranks vulnerabilities by exploitability and business impact, helping
-
- Identity and Access Management (IAM): AI continuously scores user risk levels, adapting
authentication requirements dynamically based on context and behavior.
- Identity and Access Management (IAM): AI continuously scores user risk levels, adapting
-
-
- Automated Patch Prioritization:
-
- Email Security:
-
- Natural language processing models detect sophisticated phishing emails that bypass
traditional filters by analyzing tone, intent, and metadata.
- Natural language processing models detect sophisticated phishing emails that bypass
-
- ■ Expert Tip:
-
- Start with AI-powered email security and behavioral analytics before expanding to other
AI security tools. These two areas deliver the fastest ROI for most organizations.
- Start with AI-powered email security and behavioral analytics before expanding to other
-
- ■ Expert Tip:
-
- Email Security:
AI-Powered Threat Detection and Response
AI-driven threat detection has become one of the most transformative uses of artificial intelligence in cybersecurity. Traditional SIEM (Security Information and Event Management) tools often produced an overwhelming number of alerts, many of which turned out to be false positives. This led to alert fatigue among security analysts, increasing the risk that genuine threats would go unnoticed.
AI-Powered Threat Detection in Cybersecurity: How It Works and Why It Matters
Artificial intelligence (AI) is transforming cybersecurity, and AI-powered threat detection has emerged as one of the most impactful innovations. Traditional SIEM (Security Information and Event Management) systems often generate millions of alerts, many of which are false positives. This overwhelmed security analysts, caused alert fatigue, and allowed real cyber threats to go undetected.
Today, modern AI-based security solutions solve these challenges by detecting threats faster, more accurately, and with minimal human intervention.
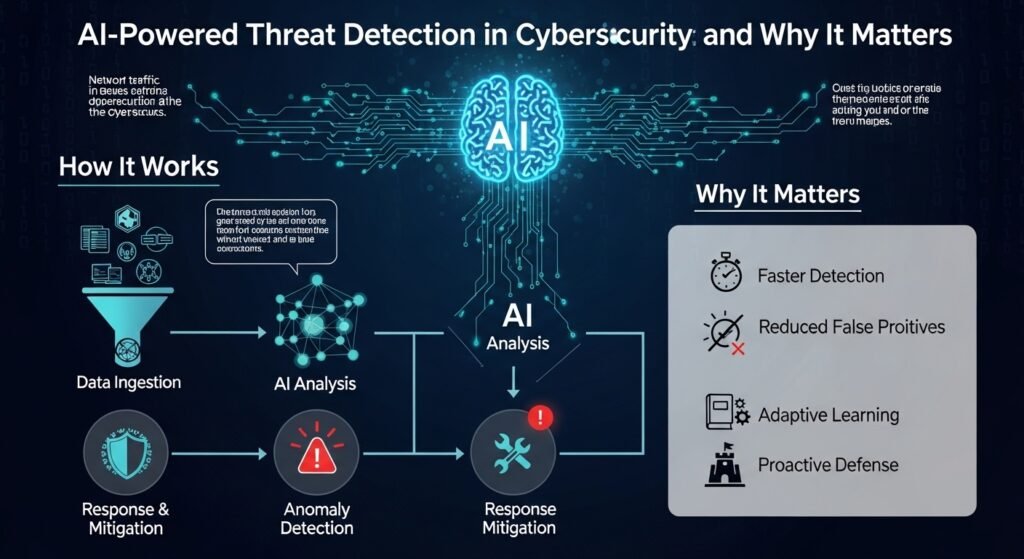
How AI-Powered Threat Detection Works
Modern cybersecurity platforms use a combination of machine learning techniques, including supervised learning, unsupervised anomaly detection, and reinforcement learning, to identify and respond to threats in real time.
1. Data Ingestion and Monitoring
AI systems continuously collect and analyze data from multiple sources such as endpoints, network traffic, cloud systems, and applications. This provides full visibility across the entire IT environment.
2. Behavioral Baseline Creation
Instead of relying on predefined rules, AI models learn what “normal behavior” looks like within your organization. This baseline is unique to each environment, making detection more accurate.
3. Anomaly Detection and Risk Scoring
Every activity is evaluated against the learned baseline. Suspicious behavior is assigned a risk score, and high-risk anomalies are flagged for investigation or immediate action.
4. Automated Threat Response
When a threat is confirmed, AI systems can automatically take action—such as isolating infected devices, blocking malicious traffic, or revoking compromised credentials—without waiting for human input.
5. Continuous Learning and Optimization
AI models improve over time through feedback from security analysts. This continuous learning reduces false positives and enhances detection accuracy.
Real-World Example of AI in Cybersecurity
In a real-world scenario, an AI-driven cybersecurity platform successfully detected and stopped a ransomware attack at a UK manufacturing company within seconds of the initial malicious activity. The system responded instantly—before any human analyst could intervene—demonstrating the speed and effectiveness of AI in modern threat detection.
Why AI Threat Detection Is the Future of Cybersecurity
-
-
-
- Faster threat detection and response
-
-
Reduced false positives and alert fatigue
Improved accuracy with continuous learning
Automated security operations
Scalable protection for cloud and enterprise environments
Machine Learning in Network Security: A Modern Approach to Threat Detection
Machine learning (ML) has revolutionized network security, enabling organizations to detect threats faster and more accurately than ever before. Unlike traditional Intrusion Detection Systems (IDS) that rely on fixed signatures, ML-based systems continuously learn from network behavior, making them more adaptive to evolving cyber threats.
As cyberattacks become more sophisticated, machine learning in cybersecurity plays a critical role in identifying hidden threats, preventing breaches, and improving overall network defense.
Key Machine Learning Techniques in Network Defense
Modern network security solutions use advanced ML techniques to analyze traffic patterns, detect anomalies, and respond to threats in real time.
1. Deep Packet Inspection with Machine Learning
Machine learning enhances deep packet inspection (DPI) by analyzing packet contents in real time. Even when malicious activity is hidden within encrypted traffic, ML models can detect patterns associated with command-and-control (C2) communications, helping stop attacks before they escalate.
2. Graph-Based Anomaly Detection
In this approach, network activity is represented as a graph of connections between devices and systems. ML algorithms identify unusual patterns such as lateral movement, unauthorized access attempts, or periodic beaconing—common indicators of cyber intrusions.
3. DNS Threat Detection
Machine learning models are highly effective at detecting malicious domains generated by Domain Generation Algorithms (DGAs). These domains are often used by malware families to maintain communication with attackers. ML can quickly identify suspicious domain patterns and block them before damage occurs.
Expert Tip: Where to Deploy ML-Based Network Security
To maximize effectiveness, deploy Network Traffic Analysis (NTA) tools powered by machine learning at critical monitoring points, including:
North-South Traffic: Incoming and outgoing traffic at the network perimeter
East-West Traffic: Internal traffic between systems within your data center
Monitoring both directions ensures complete visibility and faster detection of internal and external threats.
Why Machine Learning Is Essential for Network Security
Detects threats in real time
Adapts to new and unknown attack patterns
Reduces reliance on static signatures
Improves accuracy and reduces false positives
Strengthens overall cybersecurity posture
The Dark Side of AI: How Hackers Are Exploiting Artificial Intelligence in 2026
While artificial intelligence is revolutionizing cybersecurity defenses, it is also empowering cybercriminals in dangerous ways. The same AI technologies used to detect threats are now being weaponized to launch faster, smarter, and more evasive cyberattacks. This dual-use nature of AI is one of the most critical cybersecurity challenges in 2026.
AI-Powered Cyber Attack Techniques You Must Know
Cyber attackers are leveraging AI to automate and scale their operations like never before. Here are the most concerning techniques:
1. Automated Vulnerability Scanning with AI
Hackers now use AI tools to scan thousands—or even millions—of systems simultaneously. What once took weeks can now be done in hours, allowing attackers to quickly identify weak points in networks and applications.
2. Adversarial Machine Learning Attacks
In this method, attackers design inputs specifically to trick AI security systems. For example, malware can be modified to appear harmless to machine learning-based antivirus tools, bypassing detection entirely.
3. AI-Driven Password Cracking
Advanced tools like PassGAN use generative models to predict and crack passwords at incredible speeds. These systems learn from real password datasets, making traditional password strategies increasingly vulnerable.
4. Deepfake-Based Social Engineering (Vishing 2.0)
Cybercriminals are now using AI-generated voice and video deepfakes to impersonate executives or trusted individuals. These attacks are highly convincing and are being used in fraud schemes targeting organizations.
5. Polymorphic Malware
AI enables malware to continuously change its code structure. This constant mutation helps it evade traditional signature-based detection systems, making it significantly harder to identify and stop.
Common Mistake:
Many organizations assume their existing security tools are immune to AI-based attacks. In reality, AI systems must be regularly tested using adversarial simulations to ensure resilience.
Generative AI Is Transforming Phishing Attacks
Phishing has evolved dramatically with the rise of generative AI. In the past, phishing emails were easy to detect due to poor grammar and generic messaging. That is no longer the case.
Today, attackers use advanced language models to create highly personalized phishing emails using publicly available data from platforms like LinkedIn and social media.
These emails are:
Grammatically flawless
Contextually accurate
Highly targeted
Key Insight:
Studies show AI-generated phishing emails achieve over 50% higher engagement rates compared to traditional phishing attempts.
How to Protect Against AI-Powered Phishing
To defend your organization, implement the following strategies:
-
- Adopt AI-Based Email Security Solutions
Use advanced platforms like Microsoft Defender, Proofpoint, or Abnormal Security that rely on behavioral analysis instead of static rules.
- Adopt AI-Based Email Security Solutions
-
- Enable Email Authentication Protocols
Implement DMARC, DKIM, and SPF to reduce domain spoofing risks.
- Enable Email Authentication Protocols
-
- Conduct Realistic Phishing Simulations
Train employees using AI-generated phishing scenarios to improve awareness and response.
- Conduct Realistic Phishing Simulations
-
- Use Browser Isolation Technology
Prevent credential theft by isolating risky web sessions from your main systems.
- Use Browser Isolation Technology
AI and Zero-Day Threat Defense
Zero-day vulnerabilities—unknown flaws with no available patches—are among the most dangerous cybersecurity threats. Traditional tools fail here because there are no known signatures.
AI changes the game by focusing on behavior rather than known patterns.
Key AI Strategies for Zero-Day Protection
-
- Behavior-Based Exploit Detection
AI identifies suspicious activities like privilege escalation or memory manipulation—even if the exact exploit is unknown.
- Behavior-Based Exploit Detection
-
- Real-Time Virtual Patching
AI-powered web application firewalls can block attacks instantly, even before official patches are released.
- Real-Time Virtual Patching
-
- Deception Technology (Honeypots)
AI-driven decoys attract attackers and capture their methods without exposing real systems.
- Deception Technology (Honeypots)
-
- Continuous Automated Threat Hunting
AI constantly scans for hidden signs of compromise, detecting attacks before they escalate.
- Continuous Automated Threat Hunting
Expert Tip:
Leading teams like Google Project Zero use AI-assisted analysis to discover vulnerabilities before attackers do. Businesses can adopt similar approaches using tools like CodeQL.
AI in Security Operations Centers (SOC)
Modern Security Operations Centers are being transformed by AI automation. Traditional SOC teams often struggle with alert overload and limited resources—but AI is changing that.
Benefits of AI in SOC Environments
-
- Automated Alert Triage
AI filters and prioritizes alerts, allowing analysts to focus only on critical threats.
- Automated Alert Triage
-
- Automated Incident Response (SOAR)
AI executes predefined actions such as isolating compromised devices or collecting forensic data.
- Automated Incident Response (SOAR)
-
- Natural Language Security Queries
Analysts can search data using simple language instead of complex query syntax.
- Natural Language Security Queries
-
- 24/7 Monitoring Without Fatigue
AI systems operate continuously, eliminating gaps during nights or weekends.
- 24/7 Monitoring Without Fatigue
-
- Faster Response Times (MTTR Reduction)
Organizations report up to 60% faster response times when using AI in SOC workflows.
- Faster Response Times (MTTR Reduction)
Top AI Cybersecurity Tools in 2026
Here are some of the leading platforms shaping modern cybersecurity:
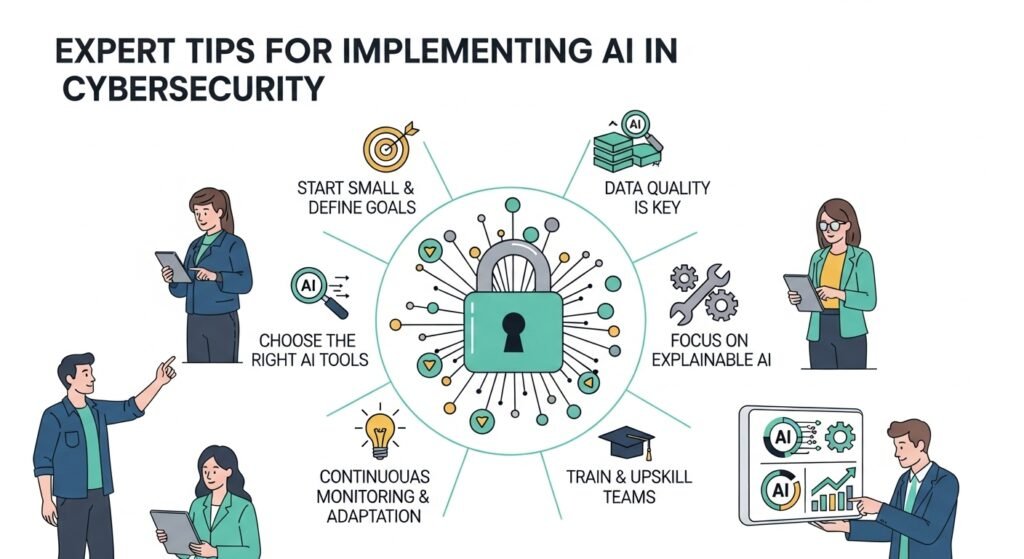
Expert Tips for Implementing AI in Cybersecurity
To get the most out of AI security tools:
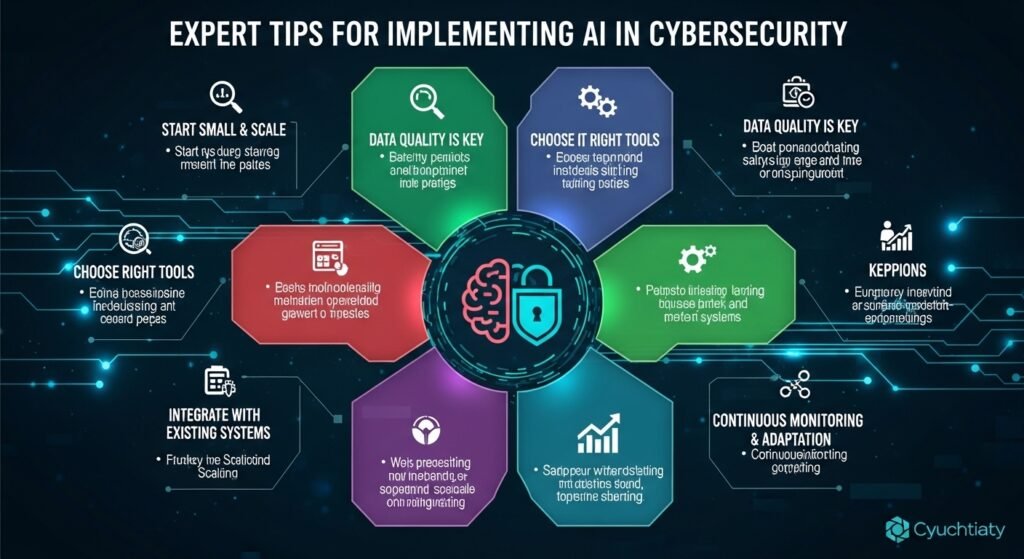
Common Mistakes to Avoid
Avoid these frequent errors when deploying AI in cybersecurity:
Treating AI as a complete solution instead of part of a layered defense
Ignoring explainability in AI decision-making
Over-automating responses without safeguards
Getting locked into vendor ecosystems
Neglecting employee cybersecurity awareness training
Frequently Asked Questions (FAQs)
How is AI used in cybersecurity today?
AI helps detect threats, analyze behavior, automate responses, and monitor systems in real time across networks, endpoints, and cloud environments.
Can AI stop all cyberattacks?
No. AI significantly improves defense but cannot eliminate all threats. Cybersecurity remains an ongoing battle between attackers and defenders.
How do hackers use AI?
Hackers use AI for phishing, password cracking, malware mutation, vulnerability scanning, and deepfake-based fraud.
What is AI-powered threat detection?
It is a method where machine learning identifies abnormal behavior and potential threats without relying on known signatures.
Is AI itself a security risk?
Yes. AI systems can be manipulated through adversarial attacks and must be secured, monitored, and regularly tested.
Conclusion: The Future of AI in Cybersecurity
Artificial intelligence is reshaping cybersecurity at an unprecedented pace. From advanced threat detection to automated response systems, AI has become an essential tool for modern defense.
However, cybercriminals are evolving just as quickly.
Organizations that succeed in 2026 and beyond will be those that.
Internal Link Suggestions
- ‘Top 10 Cybersecurity Tools Every Business Needs in 2026’ → Link from the tools paragraph in Section 2
- ‘What Is Zero Trust Security? A Beginner’s Guide → Link from the Zero Trust mention in Expert Tips
- ‘How to Protect Your Business from Phishing Attacks’ → Link from the phishing section in Section 3
- ‘AI and Privacy: What You Need to Know About the EU AI Act’ → Link from the Regulation section in Section 8
- ‘Password Security Best Practices in 2026’ → Link from the Individual Tips list in Section 6
